Quantum Cryptography: The Future of Internet and Security Management

DOI:
https://doi.org/10.54060/JMSS/001.01.004Keywords:
Quantum, Cryptography, Intractable, ConfidentialityAbstract
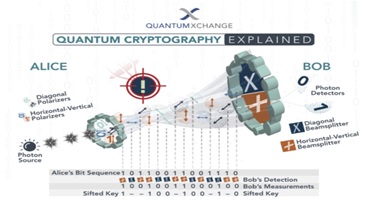
In today’s world, cryptography techniques are used and implemented on the elementary method of finding the prime factor of large integer, which is said to be “Inevitable to Track”. But living in an era where nothing is impossible to achieve, so cryptographic techniques are exposed to both technologies’ advancement in computational power of machines and advancement in the fields of mathematics to break the notion that factoring of large integers into their prime is impossible. To cope up with the threat that cryptography will face is handled by fusion of physics into cryptography, leading to the evolution of Quantum Cryptography. It is one of the fast-growing fields in computer technology. In this paper, I am going to brief the concepts of Quantum Cryptography and how this technology has led to the development of the strategy of complete secure key distribution. The paper covers the loophole present in the modern cryptography techniques, the fundamental principle of quantum cryptography, its implementation in the real world along with the limitation faced in this field, and the possible future of quantum cryptography.
Downloads
References
C. H. Bennett and G. Brassard, “Quantum public key distribution reinvented,” ACM SIGACT News, vol. 18, no. 4, pp. 51–53, 1987.
C. H. Bennett, G. Brassard, and A. K. Ekert, “Quantum Cryptography,” Sci. Am., vol. 267, no. 4, pp. 50–57, 1992.
C. H. Bennett and D. P. DiVincenzo, “Quantum information and computation,” Nature, vol. 404, no. 6775, pp. 247–255, 2000.
C. H. Bennett and P. W. Shor, “Quantum information theory,” IEEE Trans. Inf. Theory, vol. 44, no. 6, pp. 2724–2742, 1998.
G. Brassard and C. Crépeau, “25 years of quantum cryptography,” ACM SIGACT News, vol. 27, no. 3, pp. 13–24, 1996.
D. Gottesman and H.-K. Lo, “From quantum cheating to quantum security,” Phys. Today, vol. 53, no. 11, pp. 22–27, 2000.
H. K. Lo, “QUANTUM CRYPTOLOGY,” in Introduction to Quantum Computation and Information, WORLD SCIENTIFIC, 1998, pp. 76–119.
M. Khan and T. Shah, “A construction of novel chaos base nonlinear component of block cipher,” Nonlinear Dyn., vol. 76, no. 1, pp. 377–382, 2014.
W. Stallings, “Secure hash algorithm,” Cryptography and Network Security: Principles and Practice, pp. 193–197, 1999.
S. Wiesner, Conjugate coding. ACM Sigact News, vol. 15, no. 1, pp. 78-88, 1983.
C. H. Bennett, F. Bessette, G. Brassard, L. Salvail, and J. Smolin, “Experimental quantum cryptography,” J. Cryptology, vol. 5, no. 1, pp. 3–28, 1992.
“Quantum Key Distribution as a Next-generation cryptographic protocol. Andrew Campbell,” Docplayer.net. [Online]. Available: https://docplayer.net/12798486-Quantum-key-distribution-as-a-next-generation-cryptographic-protocol-andrew-campbell.html. [Accessed: 11-Jan-2021].
W. K. Wootters and W. H. Zurek, “A single quantum cannot be cloned,” Nature, vol. 299, no. 5886, pp. 802–803, 1982.
D. G. Enzer, P. G. Hadley, R. J. Hughes, C. G. Peterson, and P. G. Kwiat, “Entangled-photon six-state quantum cryptography,” New J. Phys., vol. 4, no. 345, pp. 45–45, 2002.
N. Gisin, “Quantum cryptography,” Rev. Mod. Phys, vol. 74, no. 1, 2002.
G. Brassard and L. Salvail, “Secret key reconciliation by public discussion,” Lect. Notes in Computer Science, vol. 765, p. 410-425, 1994.
M. N. Wegman and J. L. Carter, “New hash functions and their use in authentication and set equality,” J. Comput. Syst. Sci., vol. 22, no. 3, pp. 265–279, 1981.
B. Slutsky, R. Rao, P. C. Sun, L. Tancevski, and S. Fainman, “Defense frontier analysis of quantum cryptographic systems,” Appl. Opt., vol. 37, no. 14, pp. 2869–2878, 1998.