Managing Cyber Security

DOI:
https://doi.org/10.54060/JMSS/002.01.002Keywords:
Cyber Security, Cyber Attacks, Cyber Security tools, cyber security trendsAbstract
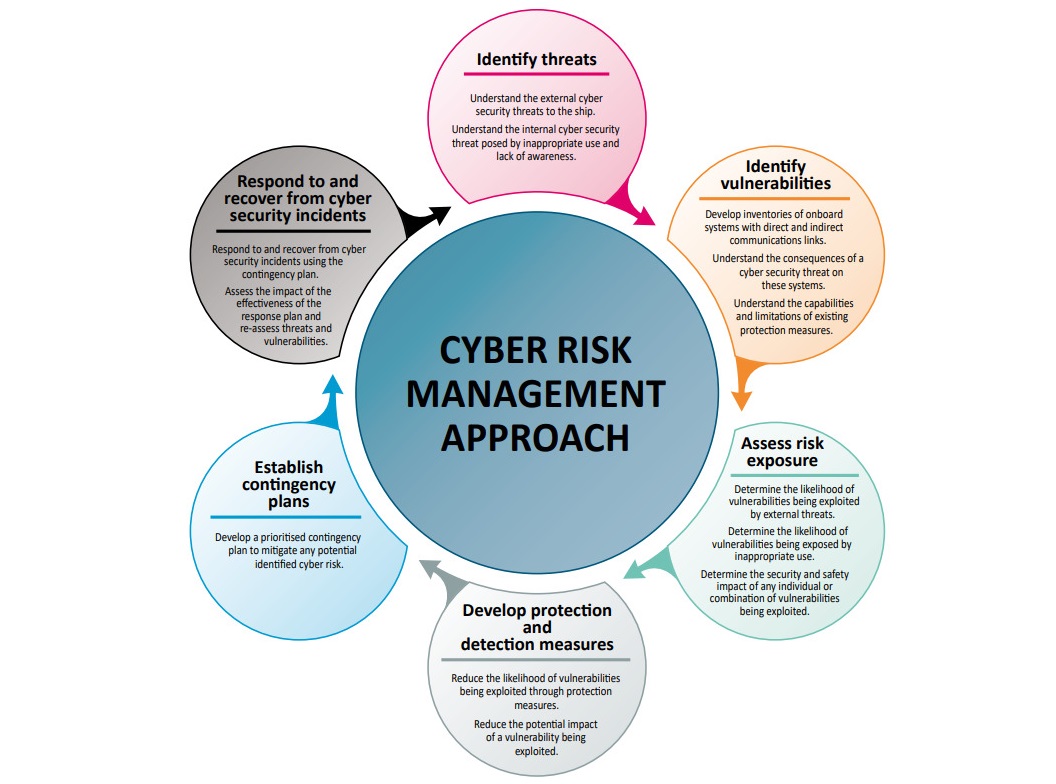
In the area of information technology, cyber security plays a critical role. In today's world, protecting information has become challenging tasks. When we think of cyber security, the first thing that comes to mind is "cyber-crimes," which are on the rise at an alarming rate. Various governments and organizations are taking a variety of steps to combat cybercrime. Despite many steps, cyber security remains a major issue for many people. This paper focuses on the issues that cyber security faces in the modern era. It also covers the most up-to-date information on cyber security tactics, ethics, and trends that are transforming the face of cyber security.
Downloads
References
P. P. Ofori, E. A. Antwi, and A. Asante-Oduro, “The behavioral intention in accessing digital healthcare information on social media,” International Journal of Scientific Research in Science and Technology, pp. 510–521, 2021.
V. Chhapre, K. Vartak, "Cyber Security: Issues, Challenges and Risks", VIVA-IJRI, Vol.1, no. 4, pp. 1-6, 2021.
A. Bendovschi, “Cyber-Attacks – Trends, Patterns and Security Countermeasures,” Procedia Economics and Finance, pp. 24–31, 2015.
K. Cabaj, Z. Kotulski, B. Księżopolski, and W. Mazurczyk, “Cybersecurity: trends, issues, and challenges,” EURASIP j. inf. secur., vol. 2018, no. 1, 2018.
D. Y. Bhosale, “a study of cyber security challenges and its emerging Trends on latest technologies”, International Research Journal of Engineering and Technology, vol. 08, no. 05, pp. 2889- 2893, 2021.
M. L. Gross, D. Canetti, and D. R. Vashdi, “Cyberterrorism: its effects on psychological well-being, public confidence and political attitudes,” Journal of Cybersecurity, vol. 3, no. 1, pp. 49–58, 2017.
Hua and S. Bapna, “The economic impact of cyber terrorism,” The Journal of Strategic Information Systems, vol. 22, no. 2, pp. 175–186, 2013.
S. Kumar and V. Somani, “Social Media Security Risks, Cyber Threats and Risks Prevention and Mitigation Techniques,” International Journal of Advance Research in Computer Science and Management, vol. 4, no. 4, pp. 125–129, 2018.
K. O. Samuel and W. R. Osman, “Cyber Terrorism Attack of The Contemporary Information Technology Age: Issues, Consequences and Panacea,” International Journal of Computer Science and Mobile Computing, vol. 3, no. 5, pp. 1082–1090, 2014.
R. Sharma, “Study of Latest Emerging Trends on Cyber Security and its challenges to Society,” International Journal of Scientific & Engineering Research, vol. 3, no. 6, pp. 1-4, 2012.
M. Sreenu and D. V. Krishna, “A General Study on Cyber-Attacks on Social Networks,” IOSR Journal of Computer Engineering (IOSR-JCE, vol. 19, no. 5, pp. 01–04, 2017.
D. Sutton, Cyber Security: A Practitioner’s Guide. Swindon, UK: BCS, the Chartered Institute for IT, 2017.
O. Almutairi and N. Thomas, “Performance modelling of the impact of cyber- attacks on a web-based sales sytem,” Electron. Notes Theor. Comput. Sci., vol. 353, pp. 5–20, 2020.